In Linux, every file and folder belongs to a user and a group. In this blog post, we will discuss three different ways to find the owner of a file or folder in Linux. Let’s get started! The following Linux commands can be used to find file owner. ls -l howtouselinux # file owner is …
Linux
In Linux, deleting a file is a pretty simple process. However, there are a few things you need to know in order to delete files safely and securely. In this blog post, we will discuss 2 ways to delete files in Linux – using rm command and unlink command. We will cover everything from using …
If you’ve ever worked with ssh, you know that it can be a bit of a pain to configure. There are so many options and parameters! One way to make working with ssh a bit easier is by using an ssh config file. In this blog post, we will discuss what ssh config files are, …
Security has reached a tipping point for the IT industry. If you’re looking for an alternative to passwords, key-based authentication in SSH might be the right solution for you. This type of authentication uses a public and private key pair to verify your identity, and it’s much more secure than a password. In this blog …
What is SSH key? How do I use the SSH key in Linux? These are some of the most common questions that people have when it comes to ssh keys. In this blog post, we will answer these questions and provide examples of how ssh keys work. We will also discuss the benefits of using …
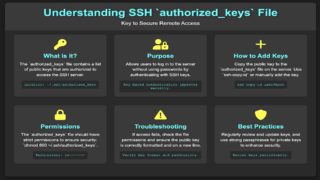
The SSH authorized_keys file is a file that contains a list of public keys that are authorized to log in to the server. This file is used to prevent unauthorized users from connecting to the SSH server. The primary purpose of this guide is to illustrate the use of the ~/.ssh/authorized_keys file. After reading …
How to list MAC address on Ubuntu Linux is a commonly asked question during a Linux job interview. Here are 3 methods to get the MAC address in Ubuntu Linux. These commands are safe to run without changing anything. Find MAC address on Ubuntu with ifconfig Get MAC address with ip link show Find MAC …
Recently we got some questions from our readers about how to check file size in Linux. How can I check the size of a file in Linux? How can I find the total size of all files and folders in a directory in Linux? How can I find out how much space a directory takes …
we can use kubeconfig configuration file to store information about different clusters, users, namespaces, and authentication mechanisms. Understanding kubeconfig A context element in a kubeconfig file is used to group access parameters under a convenient name. Each context has three parameters: cluster, namespace, and user. By default, the kubectl command-line tool uses parameters from the …
SSL Connection error is the most common error between client and server. SSL Connection error tells us that we are unable to make a secure connection with the server. It tells us what the issue is, but what makes it more difficult is that users don’t have an idea what exactly is causing this. In …